compromise assessment malaysia
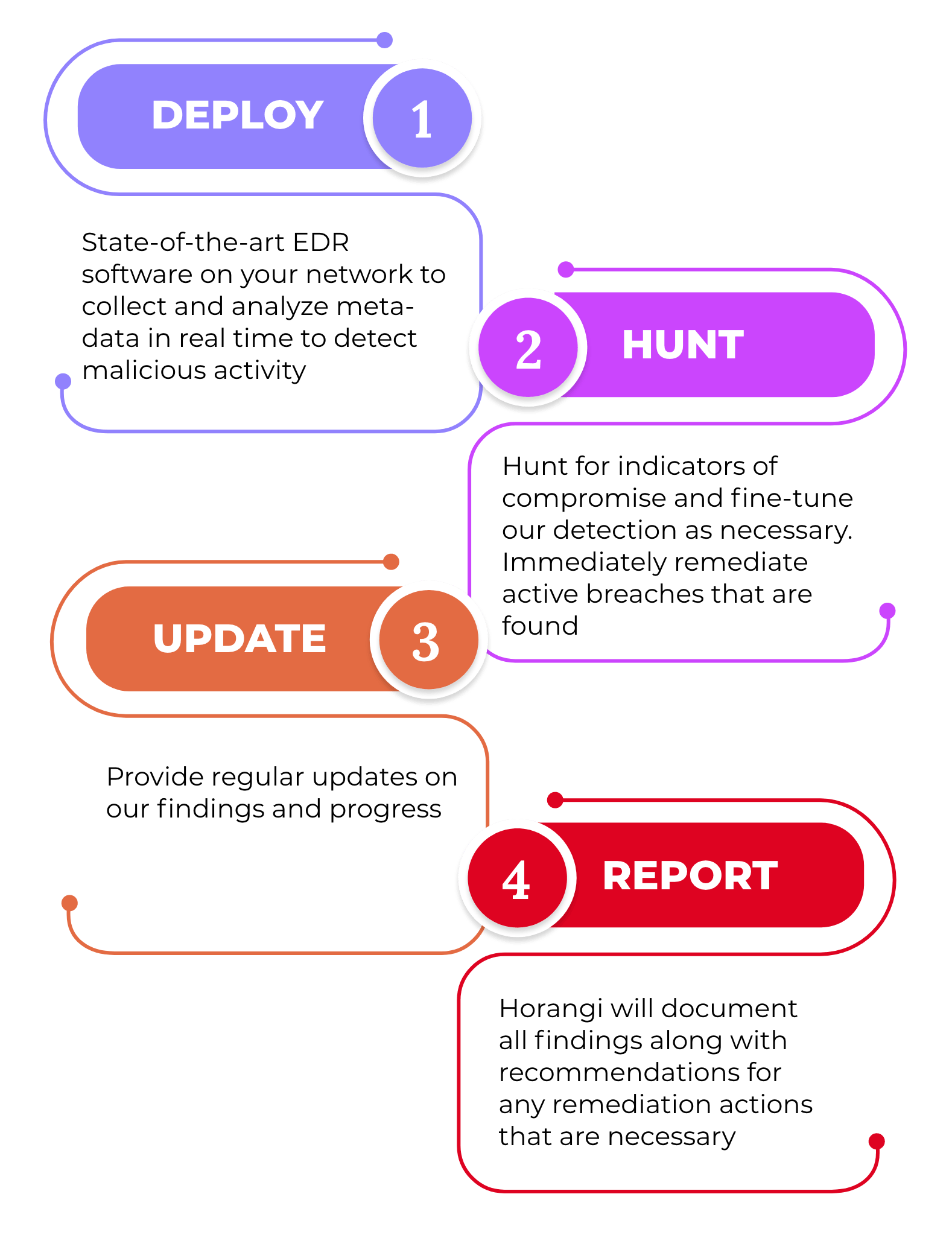
Understanding when we are breached and resolving it should be the top priority. Smart Web Level Compromise Assessment combines our deep visibility technology with our extensive experience of responding to sophisticated breaches and investigating.

Cyber Compromise Assessment Deloitte China Risk Advisory
Usually there are a few reasons companies do a Compromise Assessment.
. OTP or one-time password refers to an alphanumeric or numeric code. Performing a compromise assessment gives you confidence in your awareness of. In addition a compromise assessment can help highlight the risk associated with a compromise not being effectively communicated to seniorexecutive leadership within your organization.
Our CA service delivers a high-level review and audit of your organizations IT environment based on suspicious user behaviors logs compliances policies Indicators of Compromise IOCs or any evidence of malicious activities to identify attackers currently. Compromise Assessment checks if any attacker activity or unauthorized access is already present in your network by analyzing data logs and existing telemetry to identify. Comply with industry regulations Avoid straining customer relationships as a results of breaches and leakage of sensitive data.
2 To identify the presence of any security breaches. Our threat hunters will combine state-of-the-art targeted cyber threat intelligence network and endpoint detection to review your organizations infrastructure systems and applications in order to identify malware back-doors unauthorized access and indicators of compromise which could. We are focused on identifying the cyber attacks that these first lines of defence may have missed.
A body corporate which commits an offence under the Competition Act will attract a fine of up to Malaysian Ringgit RM 5 million while a second or subsequent offence will result in the imposition of a fine not exceeding RM 10 million. Compromise Assessment is a high-level review of the security posture of an organization to identify if they are already compromised or breached. Increasingly companies around the world understand that Compromise Assessments are a basic business imperative as they enable them to.
Malaysia through operations of branches and subsidiaries. Compromise Assessment Get an end-to-end review of your organisations infrastructure and reveal any malicious software data exfiltration unauthorised access and any other anomalous activities. In an interview with Information.
The compromised or not state of your environment your ability to identify vulnerabilities your ability to eliminate risks This is essential in running an effective SOC Security Operations Center. Compromise assessments CA answer the fundamental cyber security question Are we breached. Our compromise assessment service has been designed to answer that question.
1 To comply with local laws regulations Eg. Download Datasheet Demo To establish trust in the IT environment for the board and executives CyberStash conducts forensic-level analysis across the entire IT fleet at a. Vigilant Asia is an award-winning MSSP delivering compromise assessment services in Asia using ThreatDefence XDR platform.
Our Compromise Assessments are an essential business need for all organisations. Cybersecurity Posture and Maturity Assessment. Bank Negara of Malaysias Risk Management in Technology.
Secure Software Development Lifecycle. Cyber Security Gap Analysis and Roadmap Development. Compromise Assessment ServiceYour essential post-breach strategy for detecting systems already compromised by attacks that are too sophisticated for your existing security controls to catch.
It takes organizations an average of 191 days to identify a data breach. Our approach to Compromise Assessment The most sophisticated threat actors dedicate their time to finding ways of evading detection from traditional defence mechanisms such as antivirus. Using Deloittes Cyber Compromise Assessment CCA on your estate will help identify if there is a current or indicators of a past compromise of your network - utilising the latest threat intelligence and detection techniques.
Compromise Assessment Firmus 2020-06-14T1449110800. The approach is designed to be light-touch with simple and temporary monitoring installations. Material technology projects refers to projects which involve critical systems the delivery of essential services to customers or counterparties or compliance with regulatory requirements.
In an increasingly complex and dynamic threat landscape now more than ever organizations need to understand the effectiveness of. With a typical end-to-end duration of approximately seven to nine. While penetration tests focus on finding vulnerabilities a compromise assessment focuses on whether an organization was breached without knowing it he explains.
What Is Compromise Assessment The Benefits How It S Different How By Cycraft Technology Corp Cycraft Medium

Compromise Assessment 7 Things You Should Know Lgms Blog

Compromise Assessment Ec Council Global Services Egs

Indicators Of Compromise Definition

Indicators Of Compromise Definition
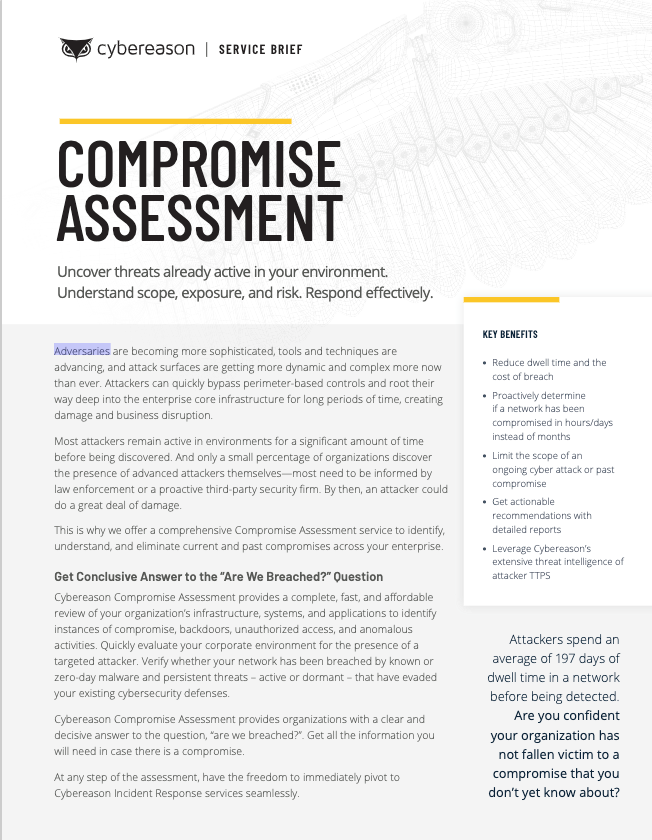
Compromise Assessment Cybereason Assessments
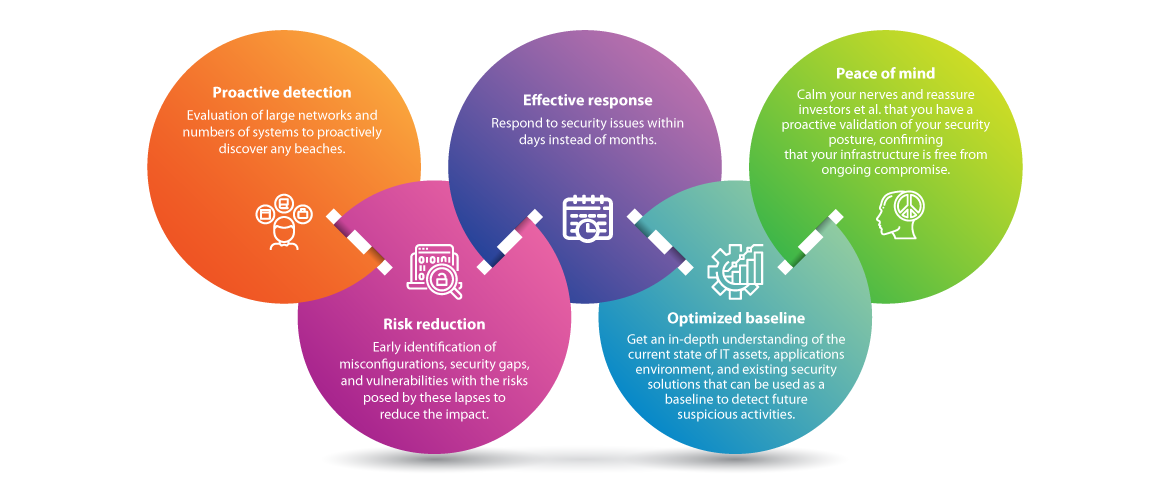
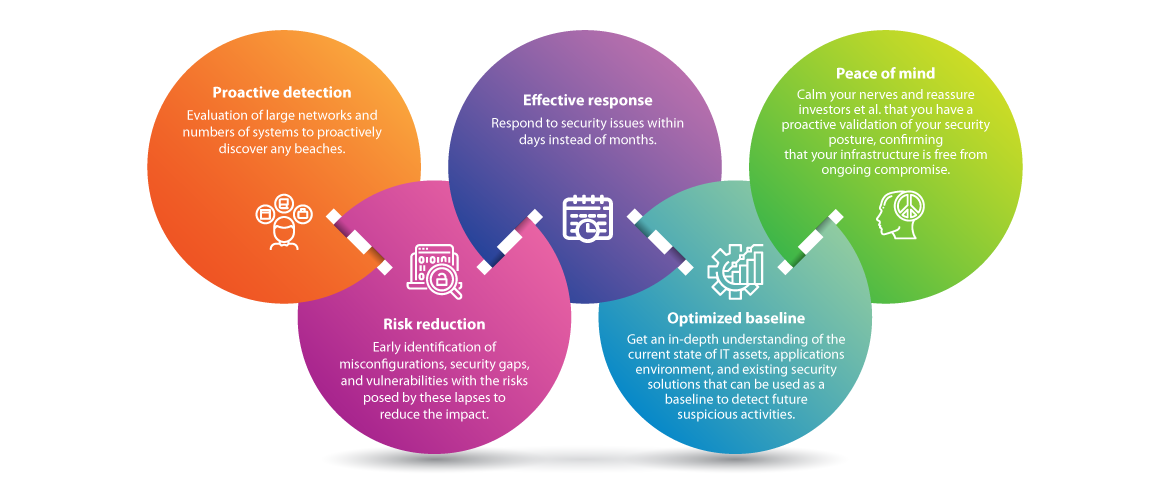
Key Benefits Of Compromise Assessment Infographic Ec Council Global Services Egs

The World Cup Is Here And With It Comes Excitement Pride Competition And Sportsm Physical Education Lessons Education Lesson Plans Physical Education Games

Compromise Assessment 7 Things You Should Know Lgms Blog

Ioa Vs Ioc Defining Understanding The Differences Crowdstrike

Compromise Assessment 7 Things You Should Know Lgms Blog

Compromise Assessment Malaysia Uncover Hidden Security Risks Firmus
What Is Compromise Assessment The Benefits How It S Different How By Cycraft Technology Corp Cycraft Medium

Compromise Assessment 7 Things You Should Know Lgms Blog

Indicators Of Compromise Definition






0 Response to "compromise assessment malaysia"
Post a Comment